Online privacy and security are eroding to say the least and because of this, many people have started using a VPN service to protect their privacy.
Aside from Security concerns, people can also use a VPN to bypass Censorship
According to a study conducted by Statista, The VPN industry is set to grow by $35.7 Billion USD by the year 2020. This is bringing in a lot of competition and this makes it harder for the end user to separate a good VPN service from the bad ones.
With that out of the way, let’s just dive in to What is a VPN and How it works?
What is a VPN?
A VPN (Virtual Private Network) lets you access the internet safely and securely by creating a secure tunnel between two devices. VPN are used to protect your data and your identity from hackers, snoopers and the spying governments.
How does a VPN work?
In simple terms, when you run the VPN software that you have purchased. It will instantly encrypt (hide) your data from the ISP and everyone who is trying to hack you. This data then goes through the VPN server to your desired online destination. The online destination then sees the location and the IP address of the VPN server instead of seeing your actual location.
Below is a graphical representation of how your connection looks with and without a VPN:
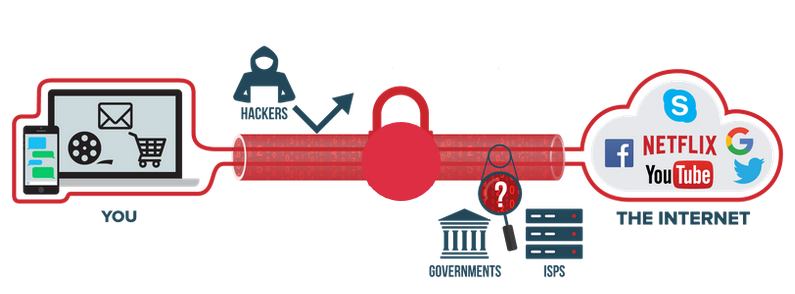
A diagram of how a VPN works.
As it has been shown in the image above, whenever you connect to the internet without the VPN your data is out there in the open. Any interested party can look at the data that you are sending from your server to another.
Usually this sort of communication isn’t very risky if you are visiting a website that’s for entertainment but it gets riskier when you are sharing or accessing sensitive data. This could be business emails or online banking, anyone one can hack and steal your data. A VPN helps you add an added security layer which makes it very difficult for anyone to hack your data.
Now that you know how a VPN works and its general purpose, let’s discuss why do you need to use a VPN?
Why Use a VPN? Why Do I need it?
There are many reasons why people use a VPN. It all depends on the situation.
- You can use to keep yourself anonymous online with the help of encryption
- You can unblock websites and bypass various geo-restrictions imposed by the government.
- Download torrents and share file with complete privacy.
- Hide your activities from the government and the ISPs.
- Change your geographical location by changing your IP address
- Browse the Internet safely over public Wifi and hotspots.
- Save money on flights and other online purchases by changing your IP Address (works for some)
These were some of the general usage of VPN services. Moving on to “Are VPNs safe?”
Are VPN Safe?
To be precise, VPNs are safe but only if they are being operated by a reliable company. The country of operations of  the VPN service also matters. If it’s being operated from a country that falls in the 5-eyes 9-eyes and 14-eyes. Then they are bound to share your data with the government.
the VPN service also matters. If it’s being operated from a country that falls in the 5-eyes 9-eyes and 14-eyes. Then they are bound to share your data with the government.
As long as you pick a VPN that is not bound by law of the country and is of high quality (using high grade encryption) you are good to go.
But what makes a VPN safe? What are the factors? There are three things you need to keep in mind in order to determine if the VPN service you have selected is truly safe.
- VPN Protocols
- Encryption
- Legal Constraints
I will briefly explain these factors in detail.
VPN Protocols
This determines how the VPN handles the data transmission from one point to another. Its level of security depends on the VPN protocol. 
There five common VPN protocols being used today. There is another sixth which is a new protocol called WireGuard which is not widely being used but it’s catching up. The five most common protocols are PPTP, L2TP, SSTP, IKEV2 and OpenVPN.
PPTP
Point to Point Tunneling Protocol is the oldest and the most basic protocol which provides good speed but bad security. It’s easy to setup but like I said before because of its security vulnerabilities it should be avoided.
L2TP/IPsec
Layer 2 Tunneling Protocol is more secure than PPTP but isn’t as fast. It uses its encryption key to create a secure connection on both end of the data tunnel but its still considered unsafe even with the addition of the IPSec protocol. In one of Snowden’s report it was mentioned that NSA has the ability to break this protocol. It’s best if you avoid this one too.
SSTP
Secure Socket Tunneling Protocol, is a Microsoft built protocol along with the L2TP/IPSec Protocol. Its connection is based on the SSL/TLS encryption which is used widely for web encryption these days. To put it simply, this is a very secure solution because of its symmetric-key cryptography. This means the only two parties involved in the data transfer can decode the encryption. But because of its tight security you will have to compromise on speeds.
IKEv2
Internet Key Exchange, Version 2 is another protocol built by Microsoft. It basically is an improved version of the previous protocols built by Microsoft. IKEv2 provides you with the best security.
OpenVPN
This is the best protocol you can use, it takes the best features of the protocols mentioned above and packs it into one and is also Open Source. This basically means that it’s being continuously improved by hundreds of developers online. Almost every VPN provider has this protocol selected by default. Because of OpenVPN’s versatility and security, this is the best protocol that you can use.
Wireguard
This is a new protocol which is basically more secure and claims to be faster than OpenVPN. Unfortunately this hasn’t been adopted by many VPN providers yet and it’s still improving on its features. What sets it apart from the OpenVPN protocol is that it’s much faster, simpler to setup and has stronger next level encryption. It uses the following algorithms:
- ChaCha20 authenticated with Poly13045
- Curve25519
- HKDF
- Blake2s
- SipHash24
Like I mentioned before, not a lot of VPN providers support Wireguard because it’s still in development. The ones that do support it are Private Internet Access, Algo VPN and AzireVPN. If you want to test this protocol out you can either buy the services of the VPN I have mentioned or you can setup your own Wireguard Server.
Because of Wireguard still being under development, OpenVPN remains the most used and popular VPN protocol in the market. Ideally you should have been able to choose any VPN protocol you want on all your devices but since most of them are owned by Microsoft they only work on Windows or PC. You will face a lot of limitations if you are an Apple user. IPhone’s default protocol is L2TP/IPSec which isn’t the safest option.
Now let’s talk about VPN Encryption.
VPN Encryption – How does it work?
This is another factor that determines if the VPN is secure or not. The most common encryption is AES (Advanced Encryption Standards) it’s a cryptographic cipher which uses 128-bit or 256-bit key length. There are other VPN ciphers which are ChaCha20, Curve25519, Blowfish and Camelia but are rarely used.
Encryption adds a key (Secret code) to the message you are sending and then transforms it into encrypted data.
The level of the VPN security depends on the type of protocols and the encryption capabilities of the VPN provider you have chosen.
Geographical and Legal Constraints
This is another important factor in determining if the VPN is safe or not! Every good VPN company will try to keep your data, information and privacy safe on the web. But they are still bound by the laws of the country they operate from, this can affect their service.
I have mentioned about the 5-eyes, 9-eyes and the 14-eyes, I’d like to explain what they are are in detail. These are countries which have signed the international surveillance alliance. These countries work together to collect and share surveillance data with each other. If the VPN service you chose operates from one of these countries then they are bound by law to share the data which goes through their server.
All I have left to say is that whenever you are looking to buy a VPN service just make sure that they don’t operate from the country that falls in the 5-eyes, 9-eyes and 14-eyes category. The list of those countries are given below:
5 – Eyes:
- Australia
- Canada
- New Zealand
- United Kingdom
- United States
9 – Eyes:
All of the 5 eyes plus:
- Denmark
- Netherlands
- France
- Norway
14 – Eyes:
All of 5 – eyes and 9 – eyes plus:
- Germany
- Belgium
- Italy
- Sweden
- Spain
In the end, the answer to the question “Are VPNs safe?” depends on the technical capabilities and the location from which it operates.
After discussing the legal aspects the next question that should arise would be….
Is it legal to use a VPN?
Yes, it is completely legal to use a VPN but there are some countries where the VPN services are Govt. controlled. These countries include China, Turkey and UAE. Which basically means you can only use state approved VPN services and anything besides those are deemed illegal. 
There are only a handful of countries that have completely banned VPN services, they are:
- Belarus
- Iraq
- North Korea
- Turkmenistan
If you are not living in the countries above, you have nothing to worry about.
Can a VPN make you 100% Anonymous?
No, but is using a VPN worth it? Yes. Without a VPN you are completely exposed and along with your ISP, Public Wifi and any server along the way can see what you are doing with the right tools. A VPN hides you from all of them and it also protects you from hackers.
Can you be tracked with a vpn?
No, you can’t and you can also double up your security if you combine your VPN service with TOR. You need to make sure you follow the steps mentioned below in order to maximize your anonymity.
- Check if they keep logs?
- The jurisdiction in which the VPN operates.
- Does it have a good encryption?
- Use a secure browser that protects you from browser fingerprinting.
- Use a good ad blocker as most of them has cookies that tracks your behavior on the internet.
You can use other privacy tools to ensure that you are not being watched while you surf the internet.
VPN Logs and their Policies
VPN logs are a collection of information your VPN client may keep to track your activity or to improve their service. Before I dive in deeper, let me define the types of logs a VPN service can keep.
- Connection Logs: These are generally ok, VPN clients keep these logs to optimize their services. This may include timestamps, connection data and IP addresses. Using this data to trace back to you can be very difficult but in an ideal situation these logs shouldn’t be kept at all. Most VPN providers delete these logs permanently after a short period of time. You can read about this in the policy page of the VPN service your looking to buy.
- Usage logs: These are the worst kind, these logs include all your data. They keep record of everything you do when you connect to their server. Generally these types of logs are kept when you are using a Free VPN which is why you should avoid them. There aren’t many VPN providers who keep usage logs as it defeats the purpose of a VPN. It’s best you go through the policies of the VPN service you are looking to buy to get a better understanding of their policies.
Now that I have explained the types of logs a VPN provider may keep, I’d like to add is that even though a VPN provider may claim to be a no logs VPN they do however keep some logs in some capacity. The key here is to go through their boring privacy policies to find out. But don’t worry I will be coming up with an extensive guide on which VPN services keeps logs and which don’t in my no logs VPN article.
Free VPN vs Paid VPN
There are hundreds of Free VPN services available in the market and all of them out of the goodness of their heart allow you to use your services for Free?!?! sounds too good to be true. Running a VPN service is very expensive, you have to pay for servers, employees, infrastructure, data centers and other things. You can’t manage all that if you aren’t getting paid! But they do get paid… a lot! by selling your data to the data mining companies and advertisers. Just like every other free social media websites like Facebook, twitter and Instagram etc. VPN services also keep your data and sell it to third parties. Though there are some Free VPNs that don’t log your activity but if you aren’t its premium member you won’t be able to enjoy the full extent of their service.
Whereas Paid VPNs aren’t that expensive on average a vpn costs around $3-5/month. There are many good cheap options available in the market. On top of that, you get to secure yourself online and have a peace of mind. You can go through my Cheap VPN article to find out which works best for you.
How do I set up a VPN?
Setting up a VPN varies from one VPN provider to another. Generally speaking setting up a VPN is easy. All you have to do is follow the instruction when you download and run the installation program if the VPN you have bought. I have listed down the general steps to setup a VPN below:
- Choose and buy the best VPN according to your needs.
- Download the VPN client on your desktop and run the setup wizard.
- Once it’s installed, login using your credentials.
- Select the server you want and click connect to regain your privacy on the internet.
Most Operating System (windows, linux, iOS, Android etc.) has their own built in capabilities but they don’t use strong protocols and are hard to set up. Which is why I recommend using the apps of your VPN provider to avoid complications.
Combining VPN with Tor
You can combine VPN with Tor if you want the ultimate privacy but this will really kill your internet speed. This is only necessary in special case scenarios for e.g. if you are a journalist and are about to break a news about a dictator from a hostile region.

But What is Tor? Tor sends your connection through a number of random nodes, while encrypting your connection at every stage. This makes it nearly impossible for anyone to track you and it’s free. All you have to do is get a official Tor web browser and you are good to go.
How do you combine them both?
- Enable you VPN connection
- Open you Tor Browser and connect with Tor.
From this point onwards, all of your data will not only be protected by a VPN but also by Tor. But like I said before this will kill your Internet speeds dramatically.
Kill Switches and How they protect from IP Leaks
IP Leaks, DNS Leaks and WebRTC leaks are serious problems. This can happen due to a number of reasons but it can reveal whatever you have been doing up until the leak happens. A DNS leaks happens when your DNS requests leak and are processed by your ISP. This reveals your IP, browsing history and your location.
IP leaks are simply when you IP is revealed due to your VPN, browser or any app you might have installed. The most common leaks are of the IPv6 Address.
Lastly, WebRTC leaks when your Chromium-based browser (Firefox, chrome, brave) that uses WebRTC APIs exposes your IP.
This is where a Kill Switch comes in handy, this kills your internet connection as soon as there is a drop in the encryption. This helps a lot when you are torrenting and you don’t want your ISP or the government to know about your activity.
Almost every good VPN provider has a kill switch, all you have to do is check if its enabled every time you connect through a VPN.
Some of the well known VPN services with Kill Switches are ExpressVPN, PIA, NordVPN, VyprVPN.
Is Torrenting safe with a VPN?
The short answer is, Yes. But it also depends on the service you are using. Every VPN provider has a different policy when it comes to torrenting, you will have to go through them in order to find out if they support it. It also depends on the type of files you are downloading, if the files are legal then you don’t have anything to worry about, if not then you might get in to trouble if you aren’t using a VPN.
You should also check if the VPN service you are using is keeping logs. If there is even a slightest hint of them logging your activity, stay away from them.
Also, you should always choose a VPN that has the Kill Switch feature. Kill switch kills your internet connection as soon as your IP or DNS leaks. If your VPN doesn’t have a kill switch option then all of your torrenting activity will be up for grabs by your ISP. Always pick a VPN that has the kill switch feature.
You need to check the download speeds of the VPN provider before you buy a torrent VPN. Needless to say, this is an important factor as you don’t want to wait too long for your files to download. In order find the fastest VPN for torrenting you will have to read my guide on it.
Setting up a VPN on a Router
I have talked about setting up a VPN on routers in my VPN Routers guide you can read it to get a better understanding. Setting up a VPN on your router isn’t that difficult and some VPN providers like ExpressVPN has launched their own pre installed VPN routers.
There are many benefits of using a VPN on router. Once you install a VPN it protects all of your devices connected to that router. This makes it very easy to manage, all you have to do is pick a good VPN and a router that supports a VPN.
The fastest VPN router available in the market Asus GT-AC5300 (1,800 MHz – quad core with AES-NI) it costs around $348 on Amazon.
How to choose a VPN
Now comes the part where you get to decide which VPN you want to buy. Choosing a VPN is simple once you know the basics of how it works and what you need it for. I am going to list down some important factors you need to consider before buying a VPN.
- Choose a VPN that caters to your need. Some maybe good for privacy others maybe good for unblocking websites.
- Your VPN provider should not keep logs. Make sure you go through its policies.
- It should be in a jurisdiction that is away from the 5, 9 and 14 eyes countries.
- It should not have any leaks, always choose a VPN that has the Kill Switch feature. Make sure you test it yourself.
- Your VPN provider shouldn’t throttle your speeds too much. Make sure you put it through the test.
- Make sure it is compatible with the devices you are using. Ask their support and test it out yourself.
- It should have strong Protocols support (OpenVPN).
- Check the number of servers and its locations.
- Since I have emphasized a lot on testing your VPN provider yourself, make sure that it has a money back guarantee of 7-30 days. The more the better.
I know that is a lot to grasp, but fret not! I have done all of the research for you. You can check out our Best VPN page for recommendations as per your need.
Final Words, VPNs are our Last Line of Defense
The usage of VPN is on the rise for all the wrong reasons. Mass surveillance is on the rise where countries like USA, UK and Australia are implementing various laws that keep track of your activity and store all of your personal data. If you are residing in one of these countries you need to use VPN to keep yourself hidden from the prying eyes of the government.
Various corporations are blocking all sorts of websites in different countries ranging from adult sites to social media. Geo-restricting content in different countries is another factor that increases the VPN usage. There are many websites and streaming services that are still available in the US or UK. People living or traveling away from these countries cannot access these websites.
All these threats have contributed to the growth of the VPN industry and if our freedom of internet is threatened the VPN industry will grow even bigger. Its needless to say that logging in without a VPN leaves you exposed to various threats online. I am a strong advocate of keeping our Privacy safe and I encourage everyone to use a VPN for their own safety and freedom.
